Cyber threats targeting industrial environments are becoming increasingly complex. Traditional software-based security solutions—such as firewalls, VPNs, and operating system–dependent encryption tools—are no longer sufficient for OT and ICS networks.
Why?
Because industrial systems require high stability, zero downtime, and absolute protection from cyber intrusion.
This is where hardware encryption devices enter the picture.
One of the most advanced examples is the EMX-6, which offers hardware-level encryption, traffic filtering, and complete isolation from OS-based vulnerabilities.
What Is a Hardware Encryption Device?
A hardware encryption device is a dedicated, OS-less system designed to:
Encrypt data at the hardware level
Filter network traffic
Establish secure, point-to-point communication tunnels
Protect industrial networks against cyberattacks
Unlike software solutions, hardware devices:
Cannot be infected by malware
Do not rely on patches or updates
Operate 24/7 with consistent performance
Have no software attack surface
This makes them ideal for cybersecurity in mission-critical industrial environments.
Why OS-less Architecture Is a Game Changer
Most cyberattacks exploit operating systems.
An OS-less device like EMX-6 eliminates this risk entirely.
Benefits of OS-less design:
No ransomware can execute
No zero-day vulnerabilities
No rootkits or remote exploits
No misconfigurable software stacks
This means attackers have no entry point into the device.
How EMX-6 Securely Encrypts Industrial Data
The EMX-6 uses FPGA-based hardware to perform real-time AES-256 encryption.
Here’s how the security tunnel works:
Data enters the EMX-6
Hardware engine encrypts it with AES-256
The encrypted data is transmitted via Electrical or Optical ports
The receiving EMX-6 decrypts the data hardware-side
Original data is delivered to the destination system
This provides:
True point-to-point security
Zero exposure to network attacks
High-speed, low-latency data transfer
Advanced Traffic Filtering (IP/MAC/Port/Protocol)
Beyond encryption, EMX-6 provides full network traffic control.
It allows administrators to decide:
Which IP addresses can communicate
Which MAC addresses are trusted
Which ports are allowed
Which protocols may pass
This level of granularity is crucial for:
Preventing unauthorized access
Isolating sensitive industrial equipment
Enforcing strict security policies
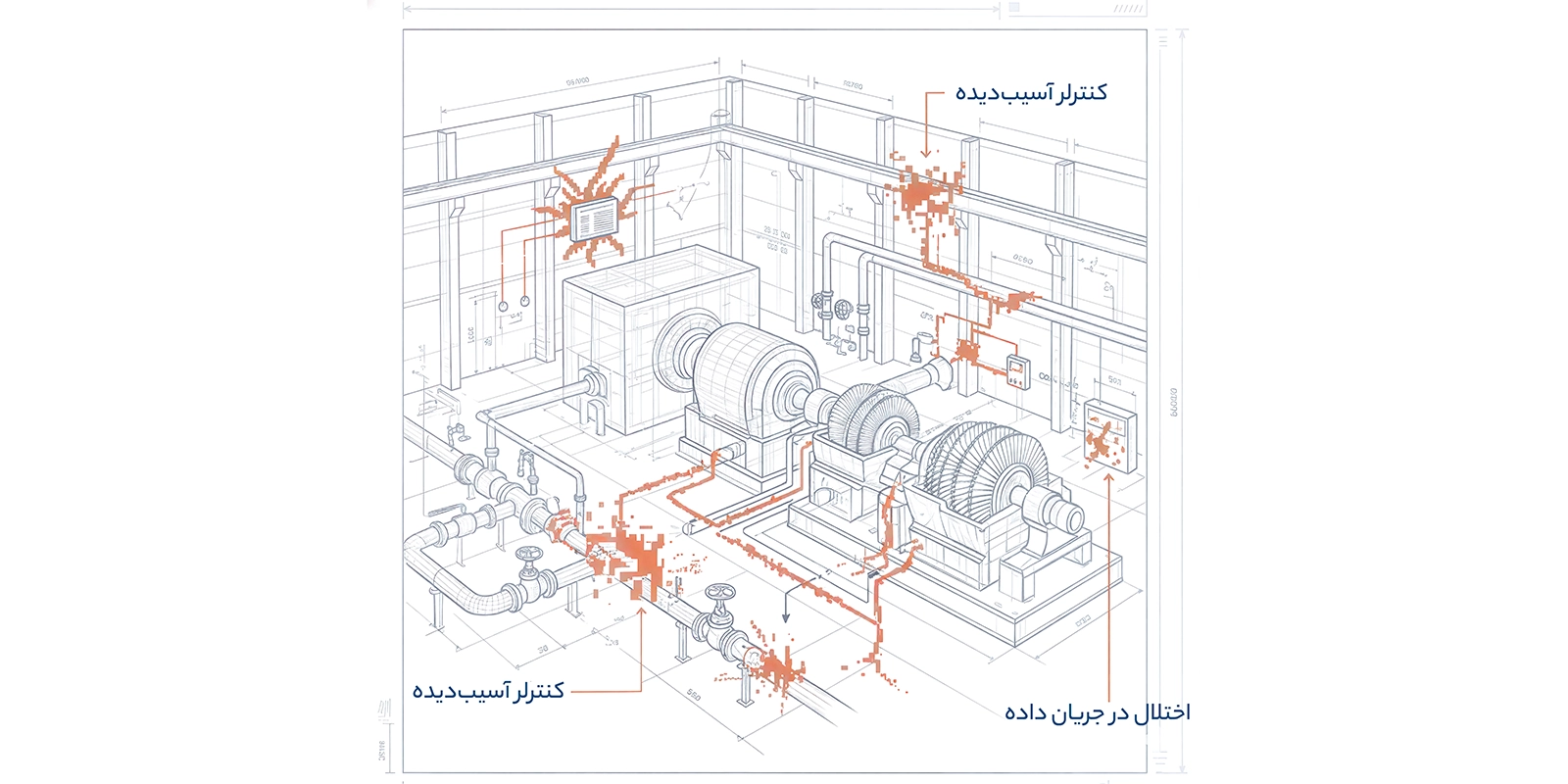
Why Industrial Networks Need Hardware Encryption
Traditional IT tools are not designed for OT environments.
Industrial networks require:
No downtime
Long-term stability
Protection regardless of software vulnerabilities
Compatibility with legacy devices
Hardware devices provide this by offering security independent of operating systems.
Industries that benefit include:
Oil & Gas
Power generation
Manufacturing
Transportation systems
Military and government facilities
SCADA & ICS environments
Key Advantages of the EMX-6 Hardware Encryption Device
1. AES-256 Hardware Encryption
Unbreakable, military-grade secure tunnels.
2. FPGA-Based, OS-less Architecture
Immune to all OS-level attacks.
3. Optical + Electrical Ports
Suitable for both short-range and long-distance secure communication.
4. Fine-Grained Traffic Filtering
IP/MAC/Protocol/Port-based filtering.
5. 24/7 High Reliability
Designed for long-term industrial operation.
6. Fully Customizable
Can be adapted to organizational requirements.
Comparing Hardware Encryption vs. Software Encryption

Where the EMX-6 Fits in Industrial Cybersecurity
The EMX-6 is ideal for:
Secure remote communication
Protecting sensitive control rooms
Encrypted industrial telemetry
Securing cross-site data transfers
Protecting SCADA/ICS environments
Building strong zero-trust architectures
Learn more about EMX-6 here:
https://pesaba.com/fa/products/ad916386-35a6-4791-90a3-7a6e181c74f7
Conclusion
As industrial cyber threats grow, organizations need stronger, more reliable security solutions.
Software alone cannot protect OT environments.
Hardware encryption devices—especially OS-less, FPGA-based systems like the EMX-6—provide:
Maximum security
High stability
Zero attack surface
Long-term reliability
This is why hardware encryption is rapidly becoming the future of industrial cybersecurity.
